To issue a Website Certificate (OWASP Top 10), we carry out a comprehensive Web Application Penetration Testing as per the testing standards and guidelines defined by OWASP (OWASP Top 10 Web Application Security Risks, OWASP Testing Guide, OWASP Mobile Top 10 Security Issues etc). As a CERT-In Empanelled Security Auditor, we are certified to be able to carry out these assessments and issue official Website Security Certificates.
Once the audit is completed successfully and all the requirements have been fulfilled, we issue a Website Security Certificate for your website.
Process for getting a Website Security Certificate (OWASP Top 10):
- Step 1 – A comprehensive level 1 audit of your website is carried out and a detailed report is provided.
- Step 2 – Once patched, the level 2 re-testing audit is carried out and all the patches and fixes are verified.
- Step 3 – The Website Security Certificate (OWASP Top 10) is issued along with relevant supporting documentation and compliance reports for your customers & partners.
Introduction to OWASP
The Open Web Application Security Project, or OWASP, is an international non-profit organization dedicated to improve the security of software.
Who needs the Website Security Certificate?
- OWASP Top is a global standards and customers across the world require a Website Security Certificate as per OWASP Top 10 standards to validate the security controls implemented by the developers.
- As per best practice guidelines and several compliance standards – OWASP Top 10 is considered to the baseline security criteria for websites.
Deliverables of the Website Security Certificate (OWASP Top 10) Process:
Importance of OWASP Top 10 Certification in Website Security
The OWASP Top 10 represents the most critical security risks to web applications, as identified by experts in the field. Testing and certifying your website against these standards isn’t just about fixing vulnerabilities; it’s a proactive step towards fortifying your digital assets against evolving cyber threats.
Risk Mitigation
The OWASP Top 10 encompasses a wide range of common security issues. By certifying your website against these standards, you’re significantly reducing the risk of data breaches, which can have devastating consequences for your business reputation and bottom line.
Building Trust
Customers are increasingly aware and concerned about their data security. A website compliant with OWASP Top 10 standards sends a strong signal about your commitment to protecting customer data, thereby enhancing trust and loyalty.
Regulatory Compliance
Many regulatory frameworks reference the OWASP Top 10 as a guideline for best practices in web application security. Compliance not only avoids potential legal ramifications but also ensures that you are on par with industry standards.
Deliverable of Our Website Security Certificate – OWASP Top 10?
- Executive Presentation: provide high level executive summaries of the engagement, key root cause analysis of the identified issues & best practice recommendations for the long-term to help leaders better understand their risk and incorporate our recommendations into their roadmap.
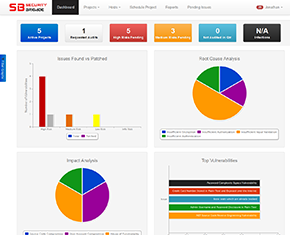
- Detailed Technical Reports: provide in-depth descriptions, step by step proof of concepts, detailed recommendations with source-code & configuration examples of all the security issues identified as part of the assessment. Security issues identified are risk-rated based on the Common Vulnerability Scoring System (CVSS) and mapped to industry leading standards such as OWASP Web Top 10, OWASP Mobile Top 10, etc.
- Safe To Host Security Certificate: The certificate of compliance is a formal document that is issued by the auditor to the organization. This document states that the organization has been found to be in compliance with the guidelines.
- List of Recommendations for Improvement: The list of recommendations for improvement will identify areas where the organization can strengthen its technology risk management framework. These recommendations can be used by the organization to improve its security posture and reduce its risk of a data breach or other security incident.