Mobile Application Penetration Testing is designed to identify vulnerabilities in your mobile apps before the attackers do. In today’s digital era, mobile applications are not just platforms but gateways to sensitive personal and corporate data.
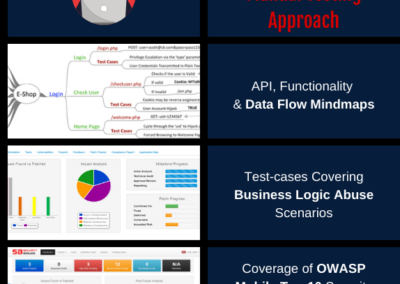
Our Approach to Mobile Application Penetration Testing
The goal of our mobile application security testing service is to fully validate your applications against all types of attacks against the core application, back-end APIs, business logic etc. Our security testing approach leverages a combination of intelligent automation that leverages AI & ML along with in-depth testing by elite teams of experts that focus on business logic testing.
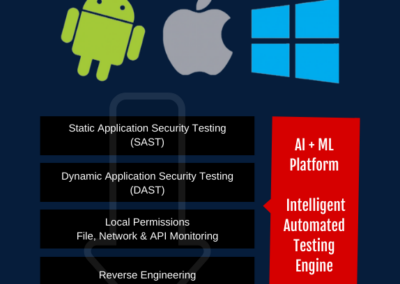
Intelligent Automation: Our proprietary AI + ML intelligent testing engine, processes each application in a sandbox environment. It includes:
- Static Application Security Testing (SAST)
- Dynamic Application Security Testing (DAST)
- Interactive Application Security Testing (IAST)
- Automated Reverse Engineering to Identify Key Processes, Components & Map Functionality
- Validation of Local Permissions, File System Access & Android API Calls.
- Expert Driven Manual Testing
- Network Security Analysis
- API Security Testing
Our elite team of experts manually review the application, its internals and its API calls to carry out a comprehensive security assessment. This includes:
The Mobile Application Penetration Testing Journey: A Step-by-Step Guide
| Project Planning | Requirement Gathering | Application Profiling |
| Automated Vulnerability Scanning | Static Analysis (SAST) | Dynamic Analysis (DAST) |
| Local Permissions & Storage | Reverse Engineering | API Logic & Data Mapping |
| Test-Case Generation | Exploitation | Engagement Analysis |
| Mitigation Strategies | Report Generation | Final Approval |
| Support | Re-Testing & Certification | Project Closure |
OWASP Mobile Top 10 Security Issues
The OWASP Mobile Top 10 is a vital resource that outlines the most common and critical security risks facing mobile applications. Compiled by the Open Web Application Security Project (OWASP), a renowned authority in the web and mobile security domain, this list serves as a key guideline for developers, security professionals, and organizations to understand and address prevalent security vulnerabilities in mobile environments.
The list includes risks such as insecure data storage, insufficient cryptography, insecure communication, and improper session handling, among others. Each category not only identifies the nature of the risk but also provides insightful recommendations for mitigating these threats. By prioritizing these top 10 issues, OWASP significantly contributes to elevating the security posture of mobile applications, helping to safeguard sensitive data against emerging threats and attacks in the increasingly mobile-centric digital landscape. This framework is not only a checklist for security assessment but also a strategic guide for developing more secure mobile applications from the ground up.
Deliverable of Our Mobile Application Penetration Testing?
- Executive Presentation: provide high level executive summaries of the engagement, key root cause analysis of the identified issues & best practice recommendations for the long-term to help leaders better understand their risk and incorporate our recommendations into their roadmap.
- Detailed Technical Reports: provide in-depth descriptions, step by step proof of concepts, detailed recommendations with source-code & configuration examples of all the security issues identified as part of the assessment. Security issues identified are risk-rated based on the Common Vulnerability Scoring System (CVSS) and mapped to industry leading standards such as OWASP Web Top 10, OWASP Mobile Top 10, etc.
- Safe To Host Security Certificate: The certificate of compliance is a formal document that is issued by the auditor to the organization. This document states that the organization has been found to be in compliance with the guidelines.
- List of Recommendations for Improvement: The list of recommendations for improvement will identify areas where the organization can strengthen its technology risk management framework. These recommendations can be used by the organization to improve its security posture and reduce its risk of a data breach or other security incident.