Network Penetration Testing is a simulated cyber attack against your network to check for exploitable vulnerabilities. In the context of network security, penetration testing is typically used to augment a web application firewall (WAF).
Types of pen tests vary—Black Box (minimal prior knowledge), White Box (full disclosure), and Grey Box (partial knowledge)—each offering unique insights. This proactive approach is a vital part of any comprehensive risk management strategy.
What is a Network Penetration Testing (VAPT)?
Network penetration testing is a security assessment that simulates an attack on a network to identify vulnerabilities that could be exploited by malicious actors. The goal of a network penetration test is to find and fix security weaknesses before they can be exploited by attackers.
A network penetration test is typically conducted by a team of ethical hackers, also known as penetration testers or pen testers. The pen testers will use a variety of techniques to scan the network for vulnerabilities
The frequency of network penetration testing will vary depending on the organization’s needs and risk profile. However, it is generally recommended to have a network penetration test conducted at least once a year.
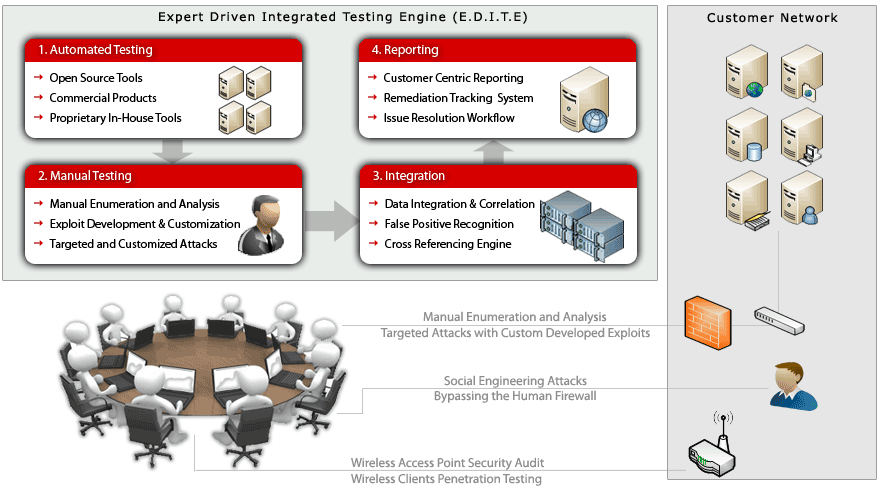
Our Approach to Network Penetration Testing (VAPT)
Our approach to Network Penetration Testing is thorough and adaptive. Combining our expert team of security analysts with cutting edge and industry leading Vulnerability Scanners, we can deliver an optimal experience for our customers. The key steps in our process are:
Vulnerability Assessment vs Penetration Testing
Vulnerability Assessment and Penetration Testing are essential, yet distinct components of a comprehensive cybersecurity strategy. Vulnerability Assessment is a broad and regular process of identifying and prioritizing potential weaknesses in a system, providing a comprehensive overview of security vulnerabilities. In contrast, Penetration Testing is a targeted, attack-simulating exercise designed to exploit these vulnerabilities, offering a real-world perspective on the effectiveness of existing security measures. While they differ in approach and focus, together they provide a holistic view of an organization’s security posture.
Regular vulnerability assessments combined with periodic penetration tests ensure a robust defense against evolving cyber threats, making them indispensable for organizations aiming to safeguard their digital assets.
Learn More about Vulnerability Assessment vs Penetration Testing.
Deliverable of Our Network Penetration Testing (VAPT)?
- Executive Presentation: provide high level executive summaries of the engagement, key root cause analysis of the identified issues & best practice recommendations for the long-term to help leaders better understand their risk and incorporate our recommendations into their roadmap.
- Detailed Technical Reports: provide in-depth descriptions, step by step proof of concepts, detailed recommendations with source-code & configuration examples of all the security issues identified as part of the assessment. Security issues identified are risk-rated based on the Common Vulnerability Scoring System (CVSS) and mapped to industry leading standards such as OWASP Web Top 10, OWASP Mobile Top 10, etc.
- Safe To Host Security Certificate: The certificate of compliance is a formal document that is issued by the auditor to the organization. This document states that the organization has been found to be in compliance with the guidelines.
- List of Recommendations for Improvement: The list of recommendations for improvement will identify areas where the organization can strengthen its technology risk management framework. These recommendations can be used by the organization to improve its security posture and reduce its risk of a data breach or other security incident.